
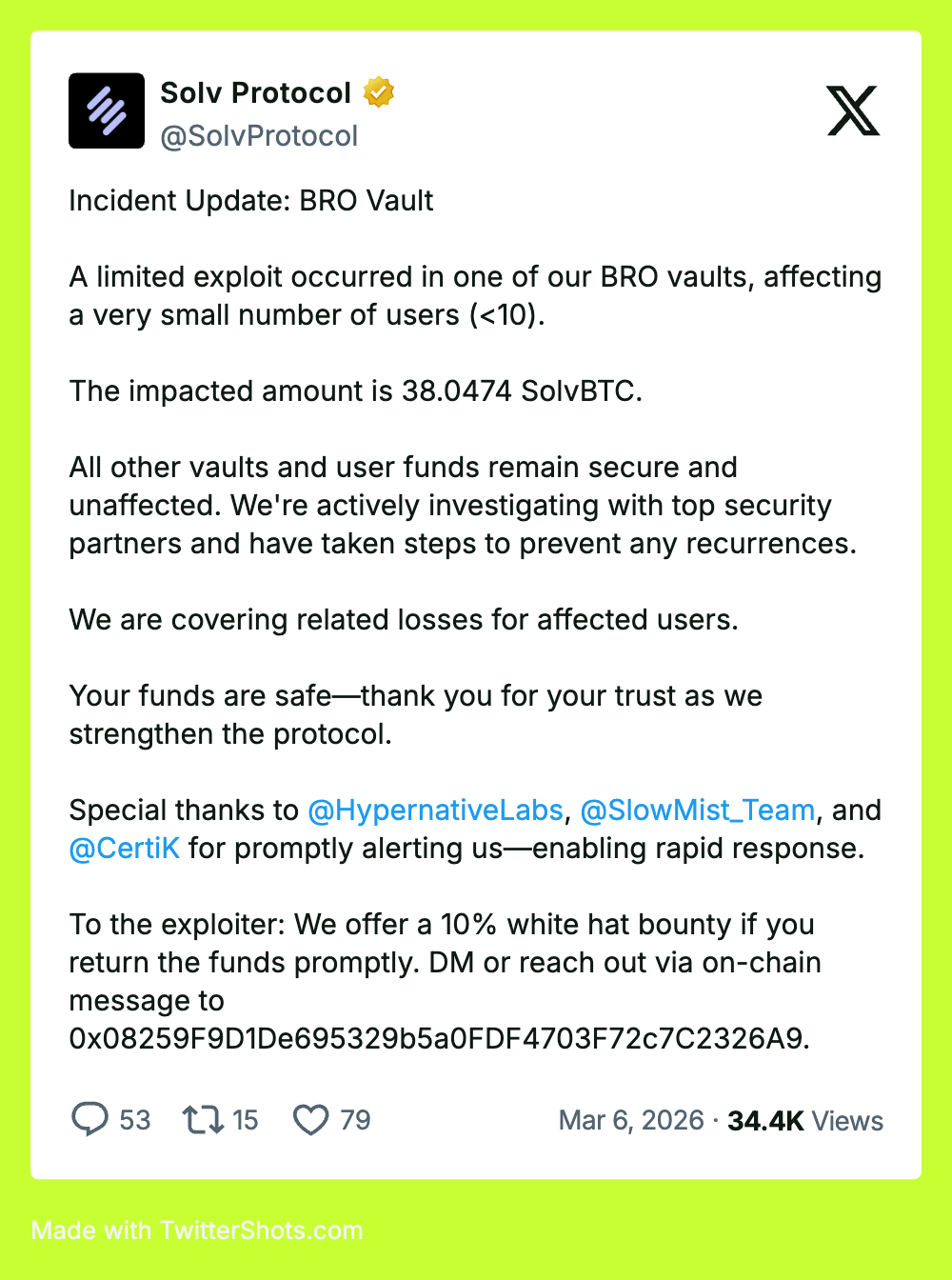
Early detection limited the blast radius of a $2.7M attack
On March 5, 2026 at 15:09 UTC, Hypernative detected an active exploit against Solv Protocol on Ethereum. Hypernative alerted Solv, which wasn't one of its customers, allowing the protocol to move fast and save an estimated $10M of funds.
The exploit targeted Solv's BitcoinReserveOffering (BRO-SOLV) contract. A flaw allowed tokens to be minted twice during a single deposit. When a user deposited GOEFS shares along with an NFT, the attacker contract transferred the NFT, which triggered the onERC721Received callback. Solv’s implementation minted BRO-SOLV tokens inside this callback before the main mint() function completed. Once the callback returned, execution resumed in mint(), which minted the same amount again. As a result, a single deposit produced two mint operations.
The attacker repeated this cycle 22 times within a single transaction. Starting with 135 BRO-SOLV, they inflated the supply to 567 million tokens (~4.2 million× amplification). The attacker then redeemed a portion of these tokens through the BRO-SolvBTC exchange, draining approximately $2.7M in SolvBTC — about 99% of the vault’s reserves.
Hypernative detected the exploit transaction when it occurred and immediately notified the Solv team. This early alert enabled the protocol to investigate the exploit, secure additional contracts, and prevent further draining of funds.
At the time of the alert, approximately $10M remained accessible to the attacker in additional Solv contracts. Without rapid detection and response, those funds could likely have been extracted in subsequent transactions.
Hackers rely on dwell time. They rely on protocols being slow, overwhelmed, or simply unaware. Multi-step attacks, cross-chain coordination, and staged withdrawals are features, not bugs, they buy time and reduce the risk of a single point of failure.
Real-time monitoring closes that window. Not completely. Not always. But enough to matter.
Although the vulnerability allowed rapid balance inflation, draining the full reserves of a protocol is rarely straightforward.
Large exploits often face practical constraints:
For these reasons, attackers frequently split exploits into multiple transactions, extracting funds incrementally.
This creates an important window where real-time detection can prevent additional losses, even after the first exploit transaction has been executed.
Reach out for a demo of Hypernative’s solutions, tune into Hypernative’s blog and our social channels to keep up with the latest on cybersecurity in Web3.
Secure everything you build, run and own in Web3 with Hypernative.
Website | X (Twitter) | LinkedIn